

Nefarious Ways
"NefyWay"
Circa. (2015-2016)
"NefyWay" was an algorithmic set of protocols on onion server(s) to specifically "break the encryption chain...",
which allowed her executable's to discover and find criminals or predatory pedophiles
-who cowardly hid behind the veil of encrypted apps and programs.

Tech*
Unlike malware such as Pegasus or phishing schemes, "NefyWay" used various algorithms and protocols on servers, initiated by the user (law enforcement, agencies, or parents). It employed specific techniques to "break" encryption chains or traditional exploits, depending on the target's device, app, or program. In 2015 and today, the encryption used by P2P apps and programs, which "NefyWay" algorithms relied upon, remains easily penetrable, simplifying the process of locating and identifying wrongdoers who attempt to hide behind encryption.

The Inconceivable Modern Reality
Since technology moves at such an impetuous or reckless murderous rate of corrigendum, versus the speed at which the laws are made to help “protect the innocent,”; the Laws are inconceivable obsolete(!)-by the time they are pressed into actions, they inevitably crumble under the definitions of the laws themselves.

Dubiously and Regrettably.....
Unfortunately back in 2015-2016, any parent who might have used "NefyWay's" platform (even if it was for Parental reassurance or to find and discover the hidden identities of their child's online anonymous pedophile), the Parents themselves were actually "breaking the law"-because of the way our current laws are written. :/
So if a parent would discover or associate with a pedophile-their stored images, pics, videos..., the Parent themselves would be "guilty-by-association" and "accused" of being a Pedophile(s) themselves. :/
Our digital laws,
which are to protect people,
are outrageously and insanely outdated.
:/
End of Line NOte:
"NefariousWays"
was just another one of my rapid R&D projects,
which I did as a knee jerk reaction
"to protect the innocent..."
Yet, because of her inherent automated function(s)
and our current "antiquated laws"...,
she was regrettably terminated
and now lives next to the
"Ark of the Covenant "...
... Eskimo ...

Soap Box:
App Developers and Companies that are responsible for intentionally making "nefarious apps," programs, or websites*1. They should be held accountable or liable for making "bad programming" or illicit Marketing decisions; especially if they have 'intentional' or collateral damage or actions, which will cause harm to children, psychological imprints, or abuse... :/
Intentionally making or designing an app(s) that have nefarious intrinsic programming or Marketing characteristics (which allow criminals & pedophiles to have easy access or associations with children-minors, or not correcting those faults, even after children have been harmed); then they are intentionally exploiting children for adult sexual and illicit gain(s); which inevitably add additional victims exponentially, all to profit from ads, links, and marketing ploys for financial or personal gain*2.
All app 'Makers' should be held accountable by their association, intrinsic actions, and applications; they innately become an "Accessory to Pedophile" as an avenue for intentional exploitation towards children and a crime by their purposeful illicit or Nefarious programming & Marketing actions; that Developer and Companies use to exploit children.
...End of Lecture...
Tech*
The standard level of " Pier to Pier " encryption (P2P) apps and programs that " NefyWay's " algorithm targeted (circa 2015/2016), was and still is (in 2021) extremely easy to breach and "break" the encryption chain... One of " NefyWay's " capabilities, was to use an automated set of "Frankenstein code(s)" to legally send unique "marking and indexing tag(s)"- with a modulating amplifying code, to inevitably fragment and " breach " the targeted (criminal or pedophile's) computer or phones app's or software's " authoritarian lines of code ", which sent a reciprocation code to instantaneously discover and identified the target (which included discovering and exploiting their Location-approximate location (network-based), Identity-find accounts on the device, Contacts-find accounts on the device, Storage-Phone-Device ID & call information/read phone status and identity, Photos/Media/Files read the contents of your USB storage/modify or delete the contents of your USB storage, Camera-take pictures and videos, Device ID & call information read phone status and identity, "Other"-receive data from Internet-view network connections-change system display settings-full network access-change your audio settings-use accounts on the device-prevent device from sleeping, modify system settings-run at startup).
Once a "Target" is identified, her secondary protocols were to verify the validity of the online user-criminal or pedophile's persona, age, etc., from within their phone's app settings and permissions. If the user's persona or age (child 0-16) did not match (within specific reasonable parameters) from the discovered settings, permissions, indexes, and now "known" Online Social Accounts "databases" like FB, Instagram, Twitter, Snapchat, Amazon, Google, etc. " NefyWay " would automatically send "traffic," "bait," or a "payload" to instantaneously inject malware, or by default "intentionally freeze-in" the target's phone, apps, associated associations, and accounts. This aids law enforcement, prosecution, evidence collection, for future legal reason (posterity), or to derive a phycological effect on the user.
Additional "Notes"
*1 Onion server or Onion routing is a technique for anonymous communication. By default, it is not indexed by HTTP severs, so you can only discoverer them if someone directly gives you the web address or by referral. Non indexed sites hopefully would prevent "bad" people from discovering and taking advantage of the system/program.
* 2. "Apps" are one-click launch programs, which may offer simplify yet sophisticated procedures, operations, websites, chat software, encrypted, or program. Still, more-over this allows developers or companies to control user content, exploit "user privacy" and gain inevitably monetary gain from the user....You. :(
*3 They will never intentional changing their Marketing and Programming characteristics, because they would rather make money from the exploitation of children; which would hamper or slow new member accounts. By adding a validation of e-mail conformation, a simple change would easily cut erroneous and bogus accounts by 92%.

NOte:
Classified and Non-Classified Material:
- Everything within this website has gone through sanitization and its contents have been altered in such a way to be deemed safe for public disclosure, and effectively prevent individuals from reverse engineering, recreating, or to prevent harm to themselves or others.
- Any three "..." (Dot Dot Dot) listed within this website means "it" has been "redacted safe"-where additional information, data, or facts that were intentionally removed, edited, or sewed for this website-as a "Freedom of Speech" public disclosure and for internet posterity.
- All Intellectual or Personal proprietary developments that I solely created, are classified or were categorized by other "Agencies," so I will continue to use and protect them with a high degree of secrecy and confidentiality; to prevent unauthorized disclosure/exposure.
- I will continue to delineate what is within the realm of Governmental SOP's, governed Civil and Military law, to prevent social psychosis.
- Notwithstanding the obvious, I am using my own discretion, to protect my own intellectual proprieties, TOADDs*, NOtes, and accompanying research, to simply prevent unauthorized recreation, but still be factually accurate.
- I will not disclose or provide any additional data-as to prevent, effectuate or employing aiding and abetting too Hacker, Terrorist, Foreign Agents, Governments, Hacktivist, WARmonger, "AI", corrupt kleptocrat, or any appointive biased narcissistic megalomania-ever again...
*TOADDs: Theoretical Observation Antecedent Derivation & Deviations
WARning:
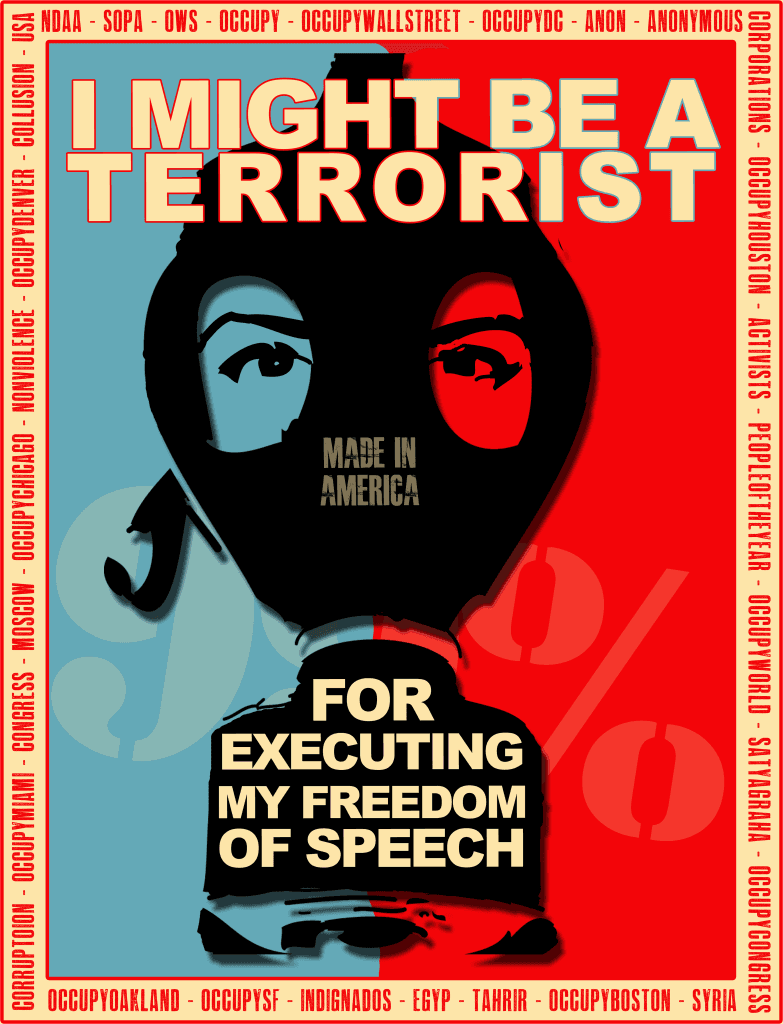
I am indemnified by my 'Freedom of Speech' protected by the First Amendment to the United States Constitution, Article 1, Section 8, Clause 8 of the U.S. Constitution, as it relates to Federal law according to 17 U.S.C. Section 102(a), the ' Freedom of Information Act ', and the Digital Millennium Copyright Act (DMCA) is a United States copyright law that implements two 1996 treaties of the World Intellectual Property Organization (WIPO).
I have never professionally worked for
the NSA, FBI, QHCG, Blah, Blah, Blah...
I always did everything "in the open" with ethical authority.
I intentionally allowed (and currently) the NSA (and others) to prob my servers, cell phones, laptops, and data files;
all in an effort to prove that I am/was NOT a Terrorist, Hacker, Foreign Agent, Hacktivist, Warmonger or Enemy Combatant.
I am just Me. :)
Copyright infringement is a civil and criminal offense. Do not recreate or copy any of my Intellectual Propriety-IP, content or data here within this website. Willful violation(s) can result in penalties beyond $100,000 per infringement. No portion of this site may be reproduced, printed, photocopied or copied by any other means of digital or mechanical reproductions, without prior written permission, from this website's owner.
FACT:
Google, Amazon, Instagram, and Facebook,
all know more about you and your "intimate privacy", than the: NSA, CIA, Homeland, FBI, GCHQ, MSS, FSB, etc..., combined!!!!! :(
Social
Fact:
Your "Right to Privacy" under the The Bill of Rights, which refers to the concept that one's personal information is protected from public scrutiny, is constantly violated by Google, Amazon, Facebook, etc.; they all abuse your trust, by collecting "private information" in the race to exploit your personal information/habits for money and profits.
This is a sad Fact! :(
Contact Me
Thank you for your interest!
I will get back to you, within the Near Distant Future; as it all depends on your personal perspective of space time, minus the mean lifetime of an 238U isotope, multiplied by the equal distance of M87's accretion disk, divided by the null flux rate of a decaying prompt neutron lifetime and multiplied by the weight of Uranus.
Mahalo :)
Oops, there was an error in the Matrix with sending your message.
Please try again later this century. Mahalo :)